As an English speaker, I mainly stick to Latin characters and some symbols that cover my day to day needs. I demand payment in £, I add a few &@! to my passwords and I am known to include the odd mathematical UTF-8 character when expressing my <3 of something. But the latin language has many more variants, IDN character support allows people from other countries to have a URL in their own language. Be it Arabic, Chinese, Cyrillic, Tamil or Hebrew. Whilst homographic attacks are nothing new, we are still a long way away from stopping them being useful to criminals.
You can use ASCII/Punycode to register domains that look like legitimate domains and it’s a concern for businesses. It aids phishing and could increase the chance you click on something you shouldn’t. This method is being used by phishers to register sites and guide users to dirty malware infested pits of doom, gathering credentials on the way there. Worryingly there doesn’t seem to be an end in sight and despite registrars attempts to limit these domains their filters can be easily bypassed.
Demo Site – https://Ǥooǥɩe.com
(site is now down and links to picture)
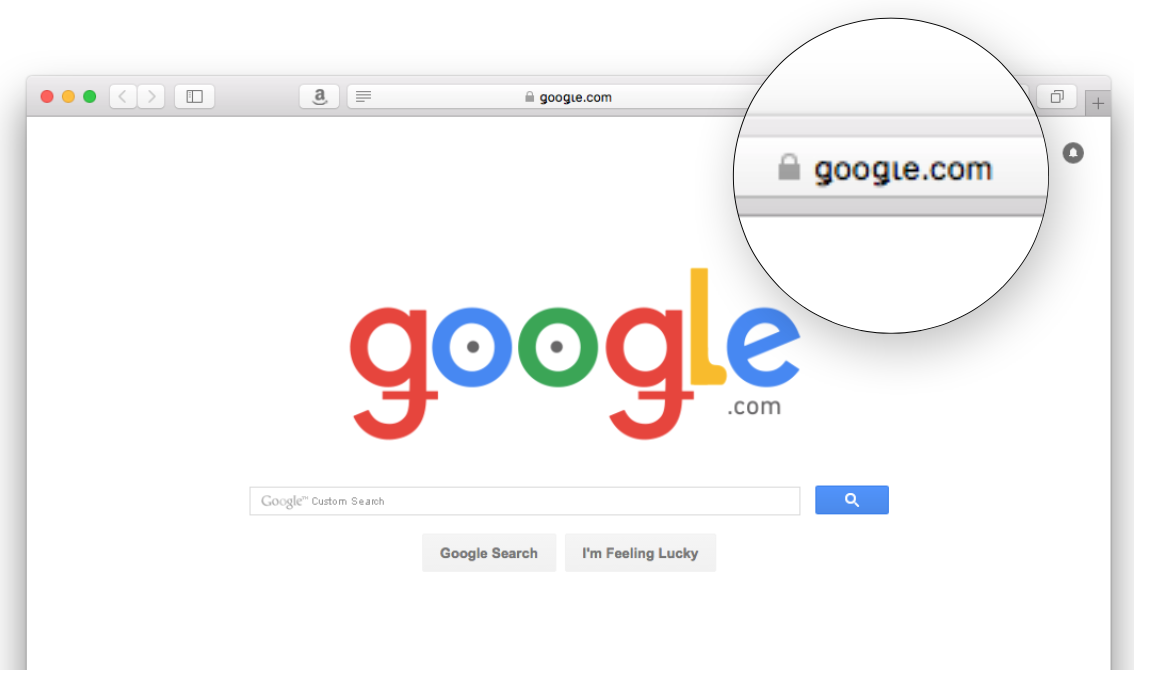
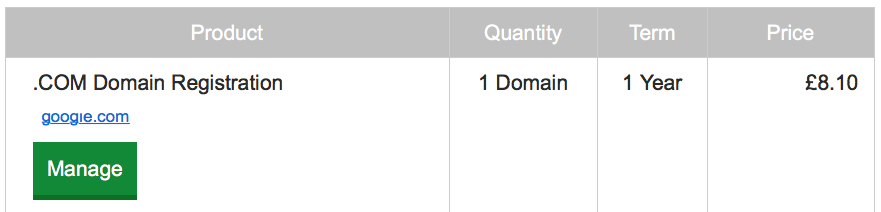
Now it wasn’t all plain sailing. The registrar seemingly didn’t decide to transfer Google.com when I tried to register the Punycode version of the legitimate domain, Verisign put a stop to that and (despite 7 calls and 2 emails) GoDaddy decided it was easier to refund me the £8.10… probably for the best… but I decided to not give up. Using a method I won’t disclose however it was trivial to register ‘xn--ooe-2fbc60f.com‘ and end up with:
The Bad
Tricking people to click on a link is wearing thin on the internet, users get savvier by the day so those with malicious intent are constantly looking for new ways to trick us. We’ve seen it with typo domains for years. A lower case ‘L‘ can look almost identical to a uppercase ‘i‘ and this abuse is common place now. The problem is with nearly all devices fully supporting ASCII Punycode characters translations you have an odd situation where it’s almost too easy to register these domains and trick people. If you think you’re on the legitimate domain and you are not, the chance of something bad happening rises.
The Fix
- I rarely state this, but the solution needs money chucking at it. Large organisations like Google know better and just buy all the combinations of similar domains the way they buy typo domains. There is nothing your humble end user can do apart from staying vigilant and look for these characters, but I guess it would be easier for large companies to just spend money buying up these domains then it would for the 3 billion internet users to constantly be on guard, paranoid of yet another attack vector.
- Domain registrars like Godaddy use Verisign to actually register a new domain with ICANN. White lists were in place a decade ago but they are not ideal, it needs work.
- Apple’s Safari browser seems to of forgotten security patches it made a long time ago and is the worst offender in displaying dodgy IDN character sets. Apple what happened to Safari security update 2005-003?
- Let’s Encrypt hours after the blog was released decided to issue certificates with Punycode. They could quite easily adopt a blacklist to disallow copy cat or typo domains from being issued an SSL certificate, but they don’t – expect a sharp rise in malicious domains making use of these free certificates.
- Google Chrome and some other better browsers will display the Punycode domain (XE–) based on a predetermined set of rules. So users might still see https://Ǥooǥɩe.com on a web page or in an inbound email but once clicking on the link it will be converted to Punycode. I think, especially if mixed language IDN characters are used, they should be guided towards a warning screen – especially if this matched a blacklist of lookalike domains. Similar to how they treat phishing sites or SSL issues.
View Our Domain Infographic



