We often talk about the unknown ‘attackers’ out to get us in the context of cyber security, but the majority of these types are not confrontational people – they barely deserve the term attacker. They hide in the shadows with their TOR browsers and anonymity supporting anonymous or whoever the favourite hacking group is that month. If you want to look at the front line of most frauds and cyber-crime in the UK, the real hardcore attackers, it’s the street smart, rock stars of the fraud world – the social engineers!
Social engineering simplified, is the practice of manipulating a mark (a victim) to align with your desired objectives, usually stealing money or information. Our business helps others form a strong resilience to this kind of attack, but the best form of defence comes from a good understanding of the process behind the crimes. So on that note, let us take a look at the stages of the UK’s most impactful type of online financial crime, that’s mandate fraud or ‘invoice diversion fraud’.
We are going to be playing the role of the criminals too, but don’t worry the bad guys are well educated on the subject already!
Reconnaissance
So what we want, our end game, is information about a target company and their relationship with another company they make or receive payments with. What does this mean in simple terms? it’s a petrol station paying regular invoices to an energy supplier. It’s an energy supplier paying fees to a government department. It’s a florist shop paying an estate agency, it’s an estate agency transferring rent payments to a property investor. These day to day transactions can be investigated and diverted – all we need to do is learn about the marks and use this information to create and personalise a quite standard attack.
To learn what we can about the target company we rely heavily on OSINT, that’s OpenSource INTelligence. The stuff people share online can be all you need to collate the information you need. The inexperienced think this is just a few quick Google searches and that’s it! but true OSINT requires searching through hundreds of unique datasets. Physical inspections by eye, live camera feeds, DVLA records, Electoral rolls, publicly available data-breaches, press statements, the dark web, Foreign online services, trademark registers, paper-based phone books, local libraries, social media, phone records – the list is endless. The higher the stakes, the more effort is going to be made. This doesn’t have to be hard though, the most powerful attribute social engineers have is their ability to look for exploitable situations. Let’s take this blog out of the dingy, unrelatable undergrowth and lets head for a fun day out at the zoo.
So whilst at the zoo and obviously after a quick look at the primates, we stumble upon some construction work going on. It sure looks impressive so we pull out our mobile phone and start performing OSINT, a task you’ve probably done several thousand times before and not realised it. We head to Google and search for “Chester Zoo Islands Construction”…
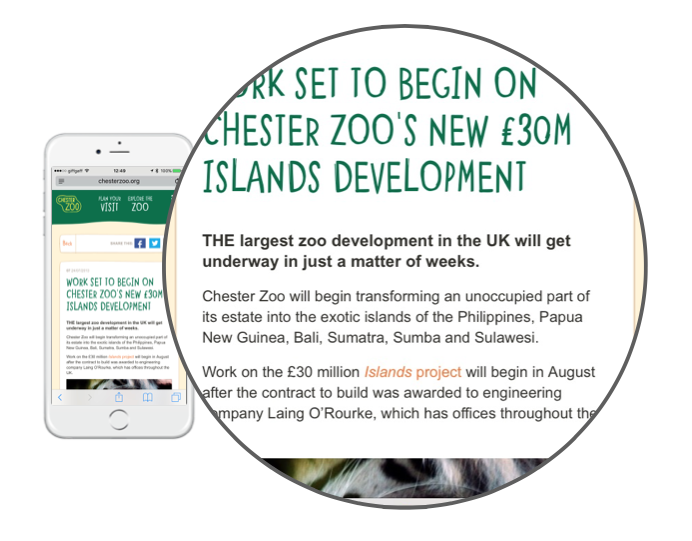
So this could be worth an attempt. We have discovered that the zoo has about thirty million pounds to spend, we know who they are spending it with now as the contractor Laing O’Rourke is stated in the press release. We know when the contract is planned to commence, we can assume a series of payments would have been scheduled for a project of this scale. So to wrap up reconnaissance all we need to do is look for the legitimate details of the finance staff at the Zoo and also the real details of the contractor’s finance department. Both of these tasks can be accomplished by perusing LinkedIn.
Conducting The Attack
So keeping this stage simple, we will plan to send a fraudulent invoice to the zoo and then follow this up with realistic prompts – such as phishing emails and vishing calls. We start by looking for domains similar to the contractor. With such a unique name this should be easy!
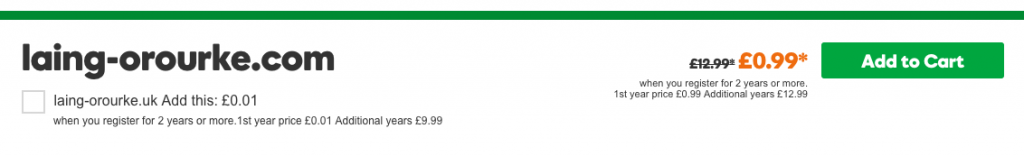
After purchase, we configure these domains to allow us to send quite realistic emails to the staff at the zoo. We need to perfect our email signature and ideally, would like a copy of theirs, so we send a perfectly innocent email to the contractor asking for a meeting or details about an event and when they reply copy it!
Next, we will use a spoofed phone number abusing the inherent flaws in caller ID systems to call the finance department of the zoo when we are ready.
So the attack starts with very little planning needed, we have the elements prepared – the next part is all luck and skill!
We send an invoice to the zoo in the mail with new banking details and a short covering letter explaining how the account was wrong on setup. The letter will have contact details in for telephones in our control and the other contact details will all be slightly different and point to us.
The next day we drop an email to the zoo’s finance team using our recently acquired domain notifying them of the change of details, we add realism by stating in the email “you should have received a letter”.
Later that day we drop a casual call into the office, by using our spoofed number they might even recognise us as the contractor:
Hi, sorry to chase this but I just wanted to confirm receipt of the change of banking details before a payment went out. You can’t be too careful these days!
At this point, all the seeds have been planted and we wait. We constantly check our bank account 24 hours a day. Days can go by and there is no money and despite all the hard work, it seems fruitless. Then out of nowhere a payment for £1,200,000 lands in the bank. Taking a second to admire the £1,200,001.64p balance the flurry to ship this money far and wide begins. Not even the most relaxed criminals think this is the end of the operation. The hardest part of an attack like this is ‘cashing out’ and making sure the innocent victim never gets the money back.
The Aftermath
Whilst this blog post might seem like the rejected script for Oceans 11, mandate fraud poses a real risk to businesses around the country. The above blog post, sadly, is based on a real event.
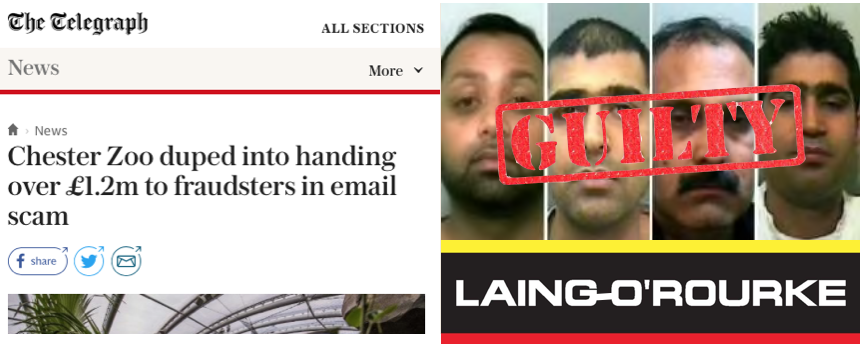
The Zoo represents the local areas best features, they employ hundreds of people, they are committed to the conservation of endangered species and they are a registered charity. The kind of criminals that target businesses is ruthless, they are individuals with no regard well-being of their victims. We see the elderly, charities and small businesses targetted every day.
Businesses, employees and the public need to be on the look out for this kind of scenario. By remembering exactly how this attack happened it will help you spot a real attack. Help spread the word through your colleagues and family – as it could happen to anyone! The above details a very large haul, but often it is far easier to steal a few thousand pounds. It’s not just phishing and million pound plots, this kind of fraud happens every day on a smaller scale – Local stores paying wholesalers, businesses paying small invoices unquestioned etc
Some Important Tips
Here are some simple tips to reduce the likelihood of being a victim of the attack.
- Learn to spot a phishing email – can you check a sender’s email address, do you know about malware and clicking links?
- Don’t trust phone numbers – numbers can be spoofed by criminals to add realism. – Read more here…
- Educate yourself about general cyber security – Use the online training tools and information, The MET Police made some videos – Check them out…
- Never feel a fool – all too often this kind of attack works because people don’t want to make a fuss. They don’t want to accuse someone on the phone of being a liar, they don’t want to ignore that email. People can be too polite and it’s because they don’t want to look a fool. Remember you can be a hero too!
- Always confirm details using a ‘safe route’ – Google the company and get the details from their website, look at your documentation in your draws. Do not trust the numbers they provide for validation.
- Test your organisation – Get independent security reviews.
- Report all frauds – Action Fraud would be the first step in reporting most frauds, but if the crime is in progress and you believe your local police force can help stop this then tell them too!