A drop box is a small computer designed to be connected to a corporate network, once connected it should enable attackers remote access to the network through a variety of methods. We have seen similar devices used in the wild take control of banking systems (link here), ATM’s and we have even seen them in Mr Robot! – we use them in social engineering penetration tests to demonstrate the impact a malicious device could have.
Over the past few years the components needed to build such a device have become popular enough to be advanced. I remember the first drop box I made using the original Raspberry Pi which was horrendously slow, it was raw and basic DD’ing (copying) the OS to the disk. At the time it relied on on a basic USB 3G dongle… which again was far from reliable. Now we have the rather zippy Raspberry Pi 3b, Lithium batteries, matching cases and everything we need direct from Amazon!
We researched the choices and opted to build a unit that would stay smallish and discreet – not necessarily covert but decent enough to not look DIY. I’ve installed such devices before on the pretext of being from an ISP or IT team and it has to be ‘smart’. The shopping list was:
- Anker PowerCore 10000 Battery Pack
- GorillaPi Raspbery Pi Case
- Raspberry Pi 3 Model B
- Hardy 2m Ethernet Cable
- 16 GB Micro SD
- Mini Heatsinks
- 2 x 128GB Micro USB Drives
We started to cobble the parts together, the power cable on the Pi is in a horrible place so we tinned a new power feed direct to the GPIO. This enables the Pi to be fed totally from one side.
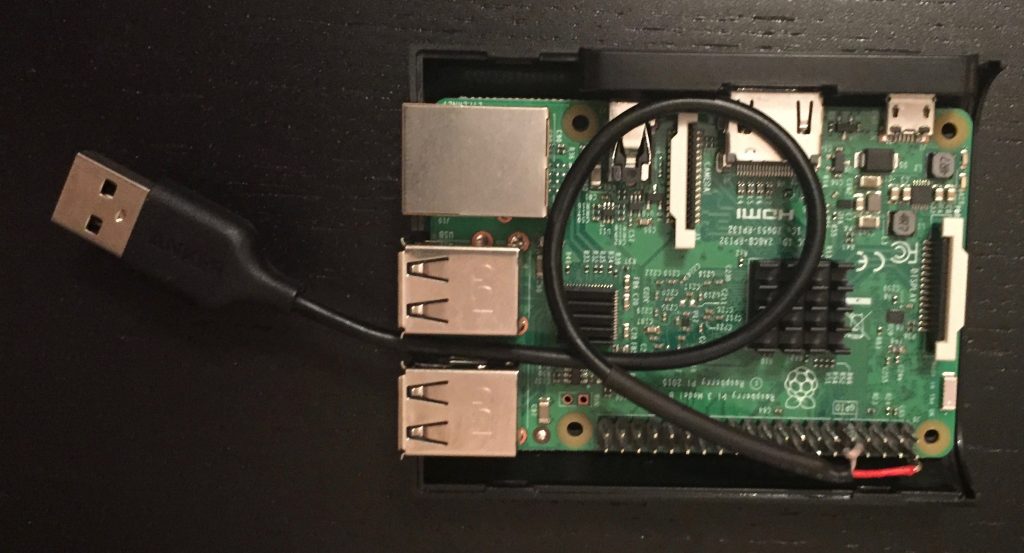
Power supply soldered to the GPIO
Next was getting the OS up and running. Almost by default I went for the Kali Linux ARM builds that are fantastic… but I wanted a device that had no hallmarks of a malicious device or one that wouldn’t spark interest if investigated. Other features like battery management, reliability and to update the SD card in a few minutes from a laptop whilst hidden in a cupboard were more important than fancy hacking tools. Experience has also shown me to focus on reliability – fail safes, fallbacks and plan B’s because once that box is installed you will probably never see it again.
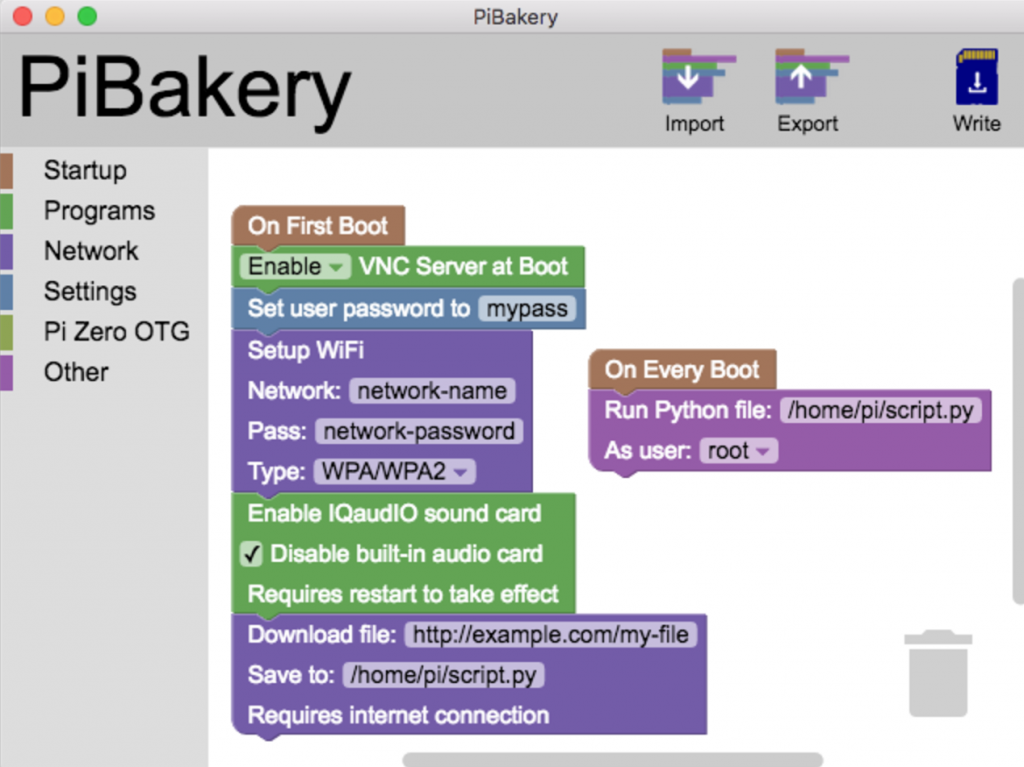
Stumbling about we found the perfect solution for our needs! It’s called ‘PiBakery‘ if you have never used this go and check it out immediately. It’s designed in a simple drag and drop style and I guess it’s main aim is to simplify the whole Pi setup. It really is funny to be inputting complex autossh commands into fields that are probably designed for kids to easily turn on a LED or something.
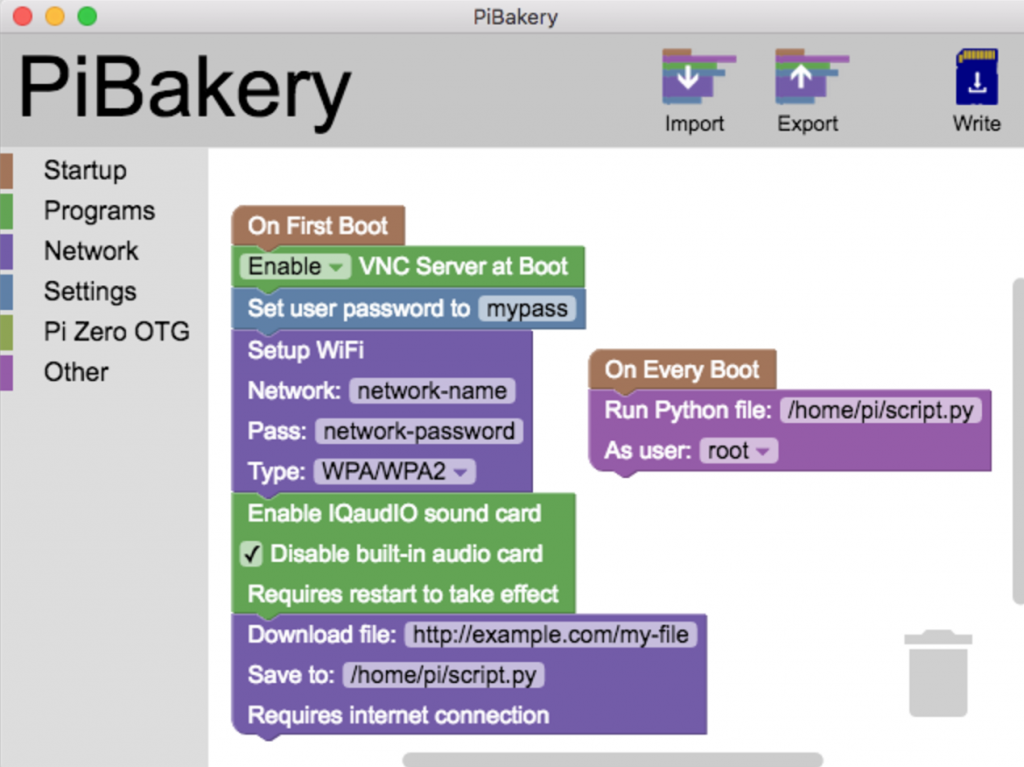
PiBakery was basic but offered amazing features suitable for penetration testing.
Once you know the desired purpose of the Raspberry Pi and have your scripts ready you simply insert a SD card and hit write – a far cry from the tedium of the early boxes. I cannot stress enough how undervalued such basic tools are for penetration testing – they just work.
You don’t have a keyboard to setup your Pi? just set it to connect automatically and SSH on!
You are a bit rusty with CRON jobs? Simply bash a few buttons!
You don’t know what init.d is?! – don’t worry about it!
The best feature of using PiBakery is that I can extract the Micro USB at any point on the test and in under 3 minutes change its configuration or actions on boot and write the changes to the card. Say you wanted a remote access point from your Pi but mid assessment you test an ethernet port and it’s disallowing SSH outbound… you don’t want to pack that device away because it’s useless – you want it in action quickly. So you insert another micro SD card in with OpenDLP to run on boot and you are back in business. This swap-ability also means if the drop box can’t get remote access on it’s own you can tell it to fall back to a 4G LTE Mobile router… basic things but options, beautiful options mid test.
The completed unit which will run for about 36 hours once installed.
The device was charged up and is now ready to be installed on a client site during a social engineering physical test. The impact of which could be devastating. On basic networks it can scan for all files and copy them to the massive USB storage. It can be used to attack domain controllers and other network devices. Once it has had it’s impact and batteries start to wither it will also exfiltrate all of it’s data to a server via SFTP either directly through the ethernet or via the WiFi hotspot hidden nearby.
How Do You Stop This?
- Disconnect unused ports in a building. If you can plug in and get an IP address in a quiet unused corner of an office – or in a building it makes it easier to install.
- If you do secure the network and decommission unused ports, the attacker will need to repurpose existing devices to gain network access – look out for network devices that weren’t there before. Extra cables going to a PC, a new box beside the printer etc.
- Wireless site surveys – often these devices will also have a hidden wireless network for easy removal of data, a site survey will monitor for such signals.
- ACL rules that blocks unrecognised devices.
- IDS devices, both networked and wireless units.