So recently I needed a computer monitor in a hurry, I was in the north and I wanted a monitor to be collected by a colleague in the south. My mind pondered several next day options but then it hit me – Argos! The nations most loved catalogue retailer had the item in stock and what’s more I could pay for this item and they could pick it up in seconds after the order! Brilliant!
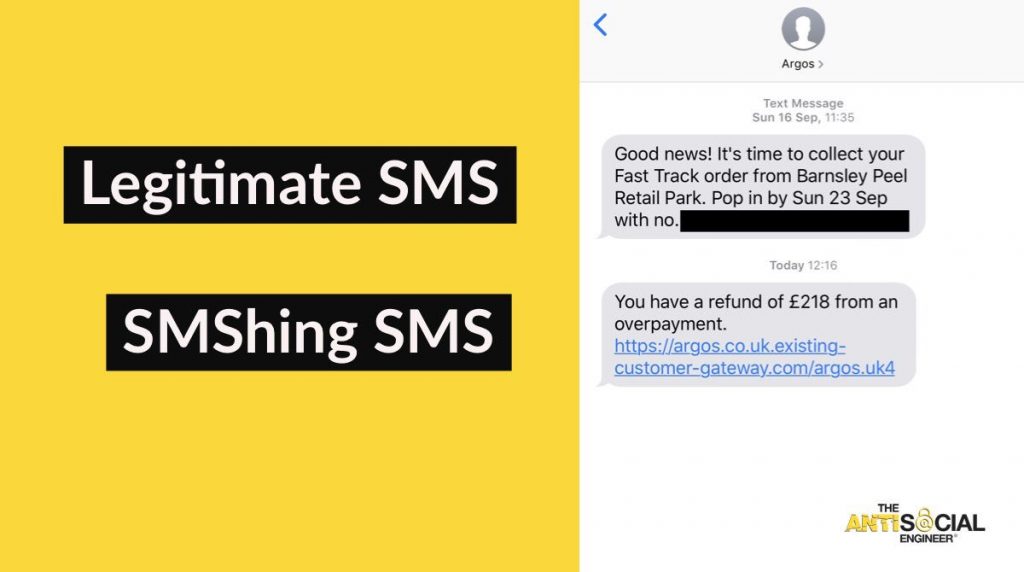
The SMShing message
Several weeks later I received a pretty convincing SMShing message (a phishing email sent by SMS) and the message alluded to a refund. It had a brilliant link in that made me very curious – and yes! I thought I had a refund for a second. It even dropped right in to the message string like a good SMShing message should.
Quick Math
For those that know me, I am hardly graced with the brain of your average mathematician, but I turned to social media to try and find a correlation and look for other recipients of the message. To our surprise it was plastered all over. People were complaining of the exact same scam message – nearly all the screenshots they were posting also displayed a previous genuine click and collect message like the one above.
5 hours recon investigation complete.
I’m calling a data breach at @Argos too much correlation in genuine customers getting a scam text after using online services.
Scammers have customers phone numbers. #Infosec pic.twitter.com/WE2vBVvZXY
— The AntiSocial Engineer (@antisocial_eng) 7 October 2018
I must say this isn’t my usual style of investigation but I was inspired by the Monzo case and how they used their data to discover and pursue a breach at a third party – surely the future of hunting for a breach!
The Scam
So this was my area… this was my jam… I understood this bit just fine. The scammers used the pretext of ‘refund’ which I found unusual, maybe you might use this closer to Christmas or seasonally but refund was interesting. It was this word that originally got my interest when I noted the SMS message. These are my points of interest on this:
- There seems to be a high correlation on social media of genuine customers that have been targetted by a SMShing message afterwards. I also used Argos online for the first time recently and afterwards received a phishing message. The messages could be sent to anyone with a phone – but there was a strong correlation in genuine customers and scam message recipients.
- The way the SMS message is worded and uses the pretext of ‘refund’ is of significance.
- The scammers do not use the exact amount of the order and opt for a generic ‘£218’ to go to all – which might indicate they have a limited data set. Maybe just telephone numbers.
- There are also instances where Argos customers have placed two online orders recently and they have had two SMShing messages afterwards. To send an SMS message costs money and it is my opinion scammers are focussing their efforts on previous customers. If they are randomly targetting people in the UK – this is of course possible. But if that was the case they would be careful not to duplicate efforts.
- The scammers were invested in this scam – proper certificates, HSTS, pretty name servers registered to them. It was done properly.
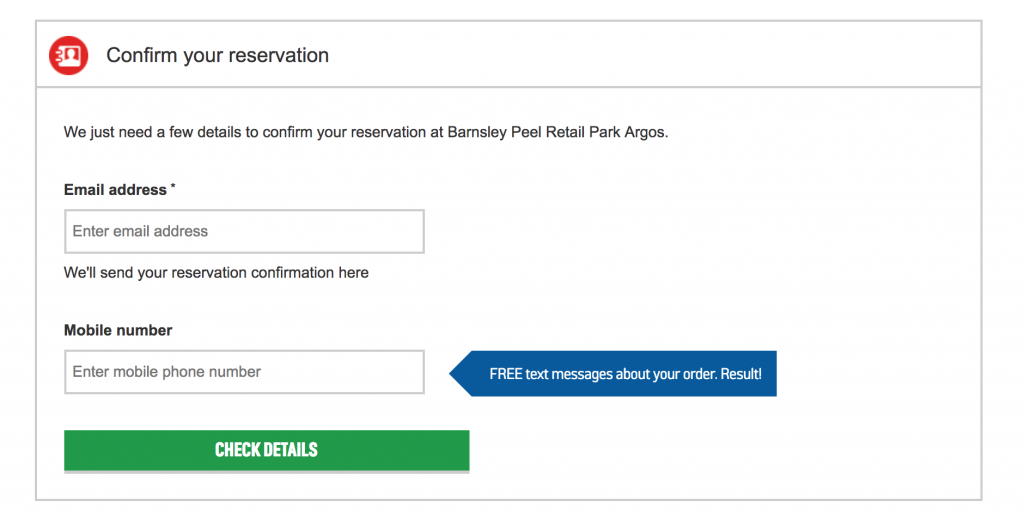
The data *could have* been sourced from their click and collect pages. ‘In correspondence with us, Argos representatives have stated this is not the case because they use HTTPS’ ?
The Denial
I reached out to their live chat agents for help on the matter, the agent pasted in a generic response and then I knew I couldn’t of been the only one that received such a copy and paste response. We have detailed the correspondence below – my issue is with the ‘just for show’ nature of their interest.
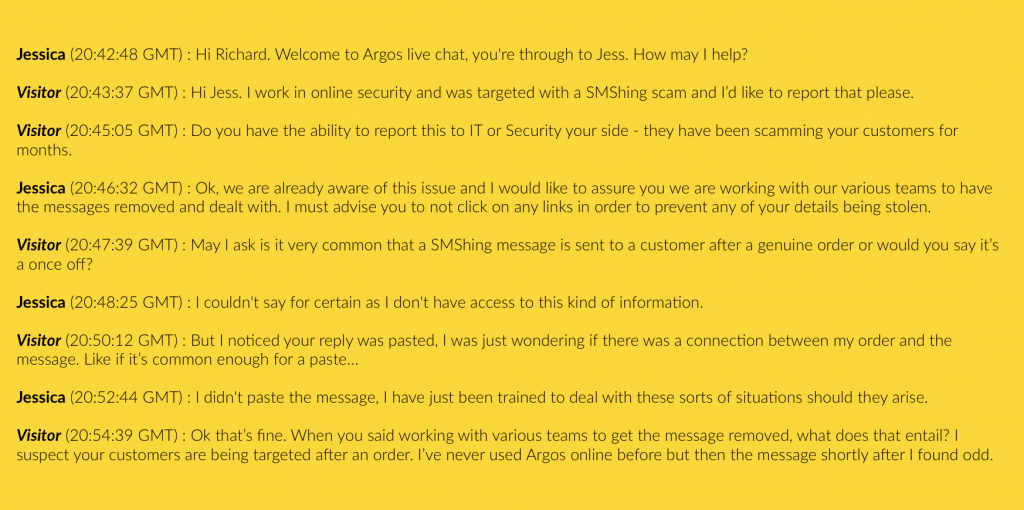
They scored A+ at generic statements but F at actually caring about what was happening or taking actionable intel.
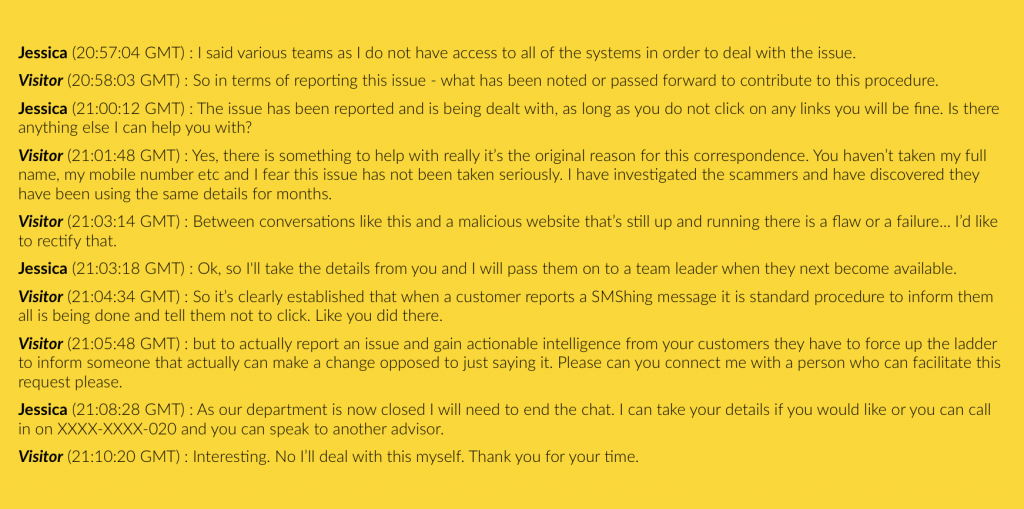
More denial and arrogance.
We sent several emails and made several phone calls to Argos, Home Retail Group (Now Sainsburys) but their stance was denial. They were the opposite of helpful. Their cybersecurity team were rude and condescending. I explained there was a correlation in victims and genuine users of their service and they did not take my concerns seriously.
Shortly after I got an email from their ‘senior media relations manager’. It’s the predictable patter of denial.
I even went as far as to explain how and why scammers could of exfiltrated genuine customers numbers (Great minds, shout out Paul Barton) and to my surprise, they started repairing the potential damage.
October 9th – The day of our email.
We emailed the Argos representative, amongst other points was the information below:
Whilst we are not employed to test your website security and provide you with consultancy, Argos have failed to build a commercial website that would be deemed safe. In the spirit of our business, allow me to explain areas of concern and detail how I suspect your potential data breach has occurred. The Argos website does not make use of a content security policy – similar to the recent British Airways fiasco. This link explains this in greater detail: https://securityheaders.com/?q=argos.com

October 10th – the day after our email.
Less than 12 hours later we see an x-frame-options header has been implemented. Maybe this is a coincidence but in a production environment – especially for a large retailer it would be a strange change. Again correlation isn’t proof, but it’s not looking good from my humble perspective.

Time for me to pipe down and Argos to explain just what went on. As a tip, think of your customers and the way they depend on your honesty – not your corporations profit!
Press statement From Argos:
“We’re aware of a number of phishing scams recently where fraudsters have targeted people posing as different major retailers. They rely on the likelihood of people having shopped with them to make their messages seem genuine.
Argos is one of the biggest UK retailers and so some fraudsters pose as us. We have been contacted about this scam by Argos customers but also people who have not shopped with us before. There has been no data breach.
We can reassure customers we take the protection of their data extremely seriously and we have a range of measures in place to ensure our website is secure. We do not disclose the specifics for obvious reasons but we have been very open about the fact any pages which contain sensitive information on the Argos website are HTTPS. This includes our click and collect pages.
We also regularly review our security measures and as part of this we have been working to move all pages to HTTPS as a precaution.” – An Argos Spokesperson.
Safe B’cos HTTPS
It’s a hard task to balance writing blogs that push companies to take security more seriously – normally in a public fashion and being an outright jerk. I try to cut it through the middle (or try) but in this instance we see their press team skirting around the facts. I do not have an issue with their HTTPS implementation – my concern was with their lack of Content Security Policy. Maybe a genuine mistake you might think… here is my last email to Argos:
“HTTPS alone will not help this issue? You haven’t grasped what I have reported. Ticketmaster had HTTPS, British Airways had HTTPS. This relates to the secure connection between a site and its users and not the content it is transmitting. Your phishing sites have HTTPS and they are no safer are they?
As previously stated you can submit a press statement as you wish. Rather than me unfairly cherry picking your previous email please come back to me with your intended statement.”
Drawing a line
Well done Argos, you’ve taken my reports on board. Listened to my whinging. Slyly updated some of your security headers in the background of this blog and issued a statement that is purposely misleading and deviates from all of my previous concerns. – classy!