When tasked with teaching employees about social engineering, the industry doesn’t half make it hard. People sat in marketing that have never sent a phishing email, or set foot in an office with a key-logger in their pocket chirp up the most awful terminology and this only serves to further alienate our intended learners. I thought I’d break this down and help you get to grips with the minimum of what’s needed.
Attack Vectors
No, it’s not a nasty Adobe Photoshop issue… an attack vector is just a path, a medium that an attacker is going to use to perform malicious social engineering. It’s much more relevant to let go of the buzzwords and worry about how they’ll impact you – at least then we can do something about it right?!
Phishing Attacks
Just for those at the back of the class fast asleep, phishing is when an attacker sends you an email and it’s designed in a way that attempts to trick you.
Ignore the types. We don’t work for the NSA. We aren’t here to examine what kind of email campaign it is. I’m pretty sure you’ll have time to argue with your company CEO about it being a spear phishing email or a whaling emailing when they are packing their hopes and dreams into a cardboard box post-breach.
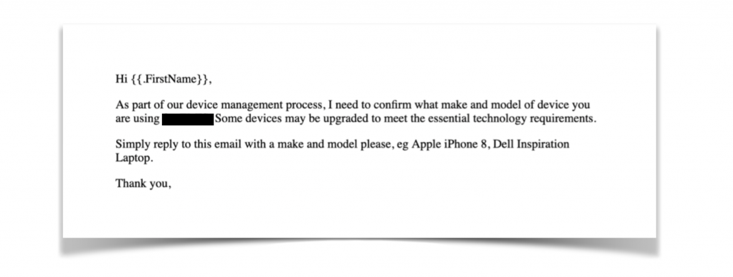
Here is the thing, we send training emails out every single day! and it doesn’t matter if it’s a simple button or a three-page letter profiled from your household rubbish – people are going to click! Hell, some of our best phishing emails don’t even have anything to click and instead rely on building rapport with the subject.
Telephone Attacks
So picture the scene, an attacker is out there with their telephone. You’re in your office doing whatever it is you do so well. How are they going to trick you and what ‘attack vectors’ are they going to use?
Well, they might send you a humble text message with a link in (SMShing) and you might click on that link and give them your password or install a malicious app on your phone. That’s one way sure… The criminals can also call (Vishing) and try to trick you with some smooth talking. Can you imagine getting a call from some loser, trying to act like he is your new line manager and you need to give them your password in a hurry… That’s as simple as a telephone attack can be – but that’s the beauty! They work because they bypass all the hustle and bustle of the office and all the protections your workplace has implemented to secure you. For a brief moment in time, it’s just them and you, mano a mano. Everything rests on what you will do with the SMS message or what you’ll say on the telephone. If you’re like me though, you didn’t come into work to duel with some hacker on a phone, so you might be caught unaware.
Physical Attacks
It’s not all geekery and black magic from a veiled corner in the world of social engineering. We head out to workplaces, admittedly often when the above techniques have failed! We try to physically obtain access to the site. No army gear or royal marine commandos stuff either, It’s just me and the trusty backpack, which contains the essentials you need for the mission. Often this is some mixed nuts, a drink and of course the laptop.
I sometimes wait outside the building and wait for someone to approach, when they unlock the door I might end a phone call and snap into action – grabbing the door before it has the chance to close. This means I can enter your workplaces using the authentication granted to the person who let me in (tailgating). When I’m there I’ll try to blend right in, all the time plugging in gadgets, placing malicious USBs on desks and hacking the WiFi.

Tiring Terms
You may find it hard to learn all the terms you’ve heard people explaining. But what if I confided in readers that myself, a consulting social engineer often have to Google some of the ridiculous terminologies I see. Terms such as ‘snowshoe spamming’ pop up and I groan reading the example some marketing graduate has invented after a 5 minute chat with a person that once sent a naughty email in 1998.
If it was essential we know the terminology to defend ourselves from cyber crime, I’d be screaming it from the rooftops – but it’s simply not that important.
Do our valued employees really need to know the definitions of all types of social engineering attack vectors? Or should we be teaching them useful defensive strategies to use in the workplace and at home, in order to defend against these attack attempts? Instead of knowing the difference between spear phishing and whaling… Do your users know how to dissect a malicious domain used in phishing emails and bogus websites? Or understand that text messages can easily appear to be from anyone and can bypass a lot of security controls?
What’s vitally important is that we learn how these criminals are affecting us with this trickery. We have our guard up when we receive a suspicious email. We politely decline to allow a stranger to enter the building behind us. These are the kind of skills that will serve to protect the organisation and keep everyone safe.
So of all the confusing things in this world, please don’t let them trick you, social engineering is not some black magic voodoo.


