When considering a simulated phishing campaign, security vendors are keen to put their best foot forward. I can’t blame them because that’s how sales and marketing work. You wouldn’t want a BMW if it wasn’t “The ultimate driving machine” would you?! There is a clear incentive for security companies to present their offerings as the best you can buy. But what if it wasn’t like this, rather than the best phishing simulation possible you were being sold the worst. You would think that would receive some criticism but we have already seen companies that purportedly bought the big cyber security brands ‘best version of themselves’ and still end up in the media for the wrong reasons. Time and time again, major problems are called out. I wanted to mix it up and sell you today the idea of the worst phishing campaign you could buy… I’ve not ‘lost it’ either, it’s a great way to educate would-be shoppers on the common dangers they should look out for. 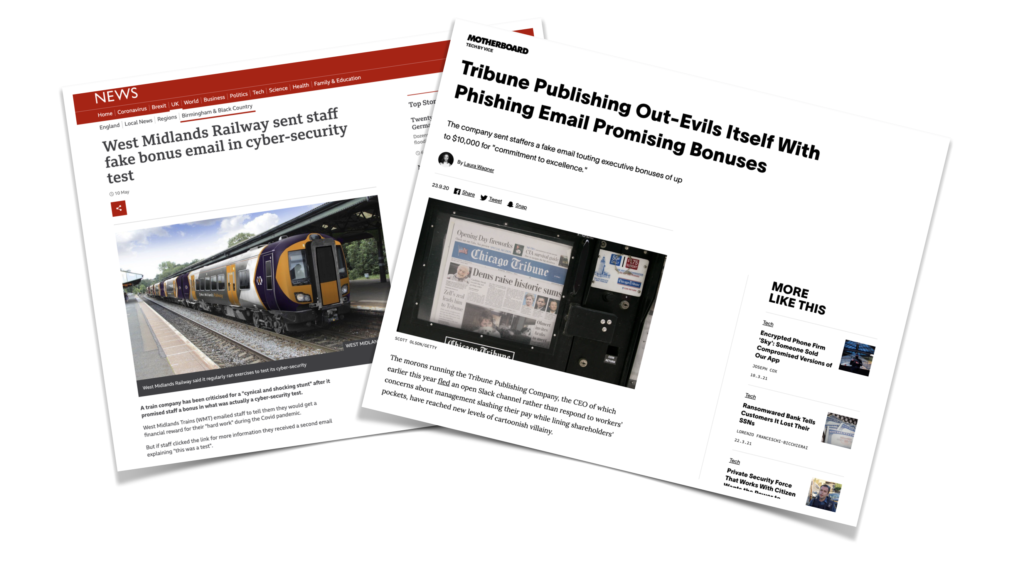
The Planning Stages
Upper management is sick of you whinging about the risk of phishing, you suggest to the board you would like to get some outsourced help in from the experts in this area. Happy to shut you up, finance allocates some budget for a phishing test, in the process of you mentioning phishing simulations and saying yes to your new budget, senior management have also hit up a few websites themselves to see what simulated phishing campaigns even are! So your budget now comes with a catch… You must inform management of the clickers so they can march around the office and call them into little meetings designed to tell employees how crap they are at spotting phishing emails. For the authority loving types within the business, this all feels like supreme power to them and there is an energy in the room akin to that moment before a good fight. HR overhear a few conversations and chime in with a few thoughts about how they could link the metrics from the phishing campaign directly to an employee’s employment record. There is a triumphant cheer from the boardroom, as people in suits genuinely think they have solved the complex issue of incoming cyber crime with standardised employee discipline techniques popular in the late ’70s.
So You Find a Vendor Online
A quick Google search for “Phishing Simulations UK” will show you the American companies offering phishing simulations in the UK, you Google again with a search for “cheap phishing simulations UK” to find companies that give initial phishing campaigns for free, followed by 16 monthly payments of £3,997.25. In the end you opt for something in the top-right quadrant of a skewed pay-per-play review site. Safe in the knowledge that no one ever got fired for recommending IBM or the information security equivalents.
You reach out to a sales team, which will usually be a bunch of commission fuelled lions dedicated solely to their bonus. Depending on your company size and the potential ROI for them, they will either keep you waiting for days before returning obscene prices via a poorly formatted Zendesk email or someone will ring you – not just once, they will add you to their Salesforce CRM under the title ‘Hot lead’ and continue to ring you at every available opportunity whilst hounding you with cringe sales focussed opening emails.
In the end, you opt for the company that is well known and also promises to stop ringing you whilst you are on the toilet if you buy from them.
Terms & Conditions
Here is where you will sign away any meaningful liability for the phishing company you chose, please check paragraph 18.7 twice it will probably state “Our engineers won’t be held liable for mistakes unless they are caught high on crack cocaine at their desk”. After some paperwork and of course a purchase order, you can forget about anything you did sign as you haven’t got a team of lawyers to interpret what it means and they have. You are comforted by the fact SuperDuperPhish™ have 204 fake reviews about how great their company is – surely a company that gets their staff to write fake reviews cares about something right?!
Whitelisting
You get told that the phishing company has to be allowed through about £35K of firewall designed to protect your company from phishing attacks because how else would they deliver the phishing simulations. You raise this security concern with them and although it would be possible to authenticate incoming emails from your vendor or add a unique mail header they are too lazy to think about your security – this is about them now.
Soon enough, test phishing emails start to come through but Microsoft still clicks the emails because the phishing company has not shown you how to genuinely filter incoming emails. The support team you have been pushed to in the absence of your account manager who has ‘moved on to new pastures’ think it’s an isolated incident and tell you not to worry despite StackExchange nerds saying otherwise.
DIY
Once testing has been completed you will be guided to a phishing portal where you will discover you have to basically do everything yourself anyway despite the license fee per user. The vendor has 900 templates to help you though, most of which are shit. 99% of the phishing email templates will be Americanised and seem out of sync with anything UK based. You complete a short yet boring training video about launching your first phishing campaign and now feel confident enough to think about your first emails going out to staff. Grabbing the IRS email template you change the logo for HMRC with your limited HTML knowledge and press fire… sorry I meant send.
You sit back and ponder the fact you are wasted in middle management IT, now you can phish people you are pretty much Jason Bourne on a secret mission and deserve some bloody respect.
Employee Feedback & Culture
Oh dear, you’ve been called into a meeting now. There is a small issue Nigel wants to discuss with you, a couple of staff have decided they think the training is unfair and seems sneaky and HR want answers. You question the reality where whole departments were egging you on phish the muggles – yet now you are the bad person when somebody raises an issue. You go off and speak to the phishing vendor and they are stumped and have no meaningful resolve for your issue because the portal you paid for is all working fine.
You take your inner hatred of all things IT and computer security back to your office and start learning about this new thing the cool kids are doing called security culture.
Fashionably late, you decide to bridge the gap between IT and everyone else via the medium of overly nice yet slightly condescending emails which inform the workforce of the details they needed to know last month. If that doesn’t solve it – it’s the staff not you don’t worry.

Ego
Annoyed that your efforts arranging the phishing project and leading the team have been shunned, you work on an email so devious, so nasty that not even the HR director themselves will know it’s a phish. You break off from learning about CSS to daydream about the future, where hopefully you will be able to call the boards attention to the fact they all clicked the link and therefore are inferior to you – the IT master.
An employee got your latest phishing email, mistook it for a genuine email about a wage increase and spent the last of their savings, content with the knowledge their pay-rise was on its way. Later on that week, shit really hits the fan when several employees that once trusted you find out it was all a lie and have leaked the story to Vice. Maybe this is the company culture you read about? bridging departments, joining the silos together. Your work so far seems to have unified the press team and legal teams anyway.
Don’t worry though. At this point, it would be common for self-doubt, but you still have 10 months left of the phishing contract so you best turn it all around. You slowly but surely learn enough about phishing, learning from all the expensive errors along the way and the quality of phishing emails improve. You get clever with the metrics too, by manipulating the complexity of emails, you can send out sophisticated phishing at the start of the year and simpler easy to spot emails at the end of the year to show a marked improvement in click rate. A true galaxy brain move right there, it may be lies but hey it shows you are good at your job.
Education
You must not actually teach employees about phishing, please remember to avoid this at all costs. Keep focused, this is a mission to make people disgruntled and flex on them. Avoid anything too woke, like drop-in sessions where people can ask about security. If anyone questions the effectiveness or efficiency of the exercise just send out a group-wide email banging on about why it’s important for them to give one flying f*ck about phishing. If they want education, tell them not to click links in the email without actually giving anything useful away, you know, like the warning signs they should look out for. Things like eLearning, posters and awareness materials will only waste their precious time spent nattering at the water-cooler. If you need to up the ante, drag them into your messy corner office and call them stupid.
Reporting
No phishing campaign would be complete without a report. As you scrabble around the phishing portal, you find the option to export a PDF of the campaign. Don’t be concerned if this looks like a Microsoft Word document opened in LibreOffice, it’s the metrics that matter. Damn, why does it say 100% of people clicked the email when they didn’t? Probably an error, those are the stats though and we shouldn’t ever question it. Everyone clicked. Move on, you are in a hurry to present the stats in your meeting.
OK OK, Being Serious
As phishing consultants, we can see the problems mentioned above from a unique perspective and we do genuinely try to avoid these issues. It’s hard to watch some of our competitors work unethically and game metrics. The NCSC themselves spoke out about phishing simulations labelling them as next to useless, no doubt because of the damage phishing companies have caused and this does seem unfair. No one ever spoke to us about phishing, despite the fact our simulations are supplied to government departments and fully managed by professionals. We feel that’s the biggest problem in the phishing industry, in the desire to scale, companies have bundled people into DIY portals and passed the buck. When a company is in the press for that horrendous template the phishing companies are never mentioned. The limelight has now been shifted to a publisher or a train company – the very people that wanted help in the first place.


